On Sunday morning, Vercel confirmed what a lot of people on X had been whispering about since the night before. Somebody got into their internal systems. The company put out a short security bulletin, pulled in outside incident responders, notified law enforcement, and told a “limited subset” of affected customers directly.
If you have never thought about deployment platforms as supply chain risk, this is the week to start.
The short version of what happened
Vercel published a short security bulletin on their knowledge base. They confirmed unauthorized access to certain internal Vercel systems, said services remain operational, and pointed customers at the sensitive environment variable feature as a mitigation. The bulletin also names a single indicator of compromise: a third-party AI tool’s Google Workspace OAuth app, ID 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com, which Vercel describes as the origin of the incident and flags for broader community investigation. That is basically the whole official disclosure.
The unofficial version, pieced together from the BreachForums listing and reporting from BleepingComputer and Decipher, is a lot louder.
An actor posting under the ShinyHunters name put Vercel data up for sale at around $2 million. The listing claims to include internal database records, employee account access, source code, GitHub tokens, NPM tokens, API keys, and access to internal deployments. As proof, the seller reportedly dumped a sample of 580 employee records pulled from Vercel’s internal Linear workspace, complete with names, Vercel emails, account statuses, and activity timestamps, plus a screenshot of an internal enterprise dashboard.
Worth flagging: BleepingComputer reports that established members of the ShinyHunters crew have denied involvement, which means the name on the listing may be borrowed rather than authentic. The data being real and the brand being spoofed are not mutually exclusive.
Theo Browne (t3.gg) posted early analysis suggesting that Vercel’s Linear and GitHub integrations took the brunt of the intrusion, and that environment variables flagged as “sensitive” (which Vercel stores encrypted and separated from standard env vars) appear to have held up. Standard, non-sensitive env vars did not get that same protection.
Vercel has not confirmed the attack vector. No timeline of when the initial access happened. No breakdown of what “limited subset” means in customer-count terms. That gap in the official story is part of why the industry reaction has been sharp.
Why this is not just a Vercel problem
Here is the thing about modern deployment platforms. You hand them your source, your build pipeline, and your secrets, and in exchange they give you speed. That tradeoff makes sense right up until the platform itself becomes the attack surface.
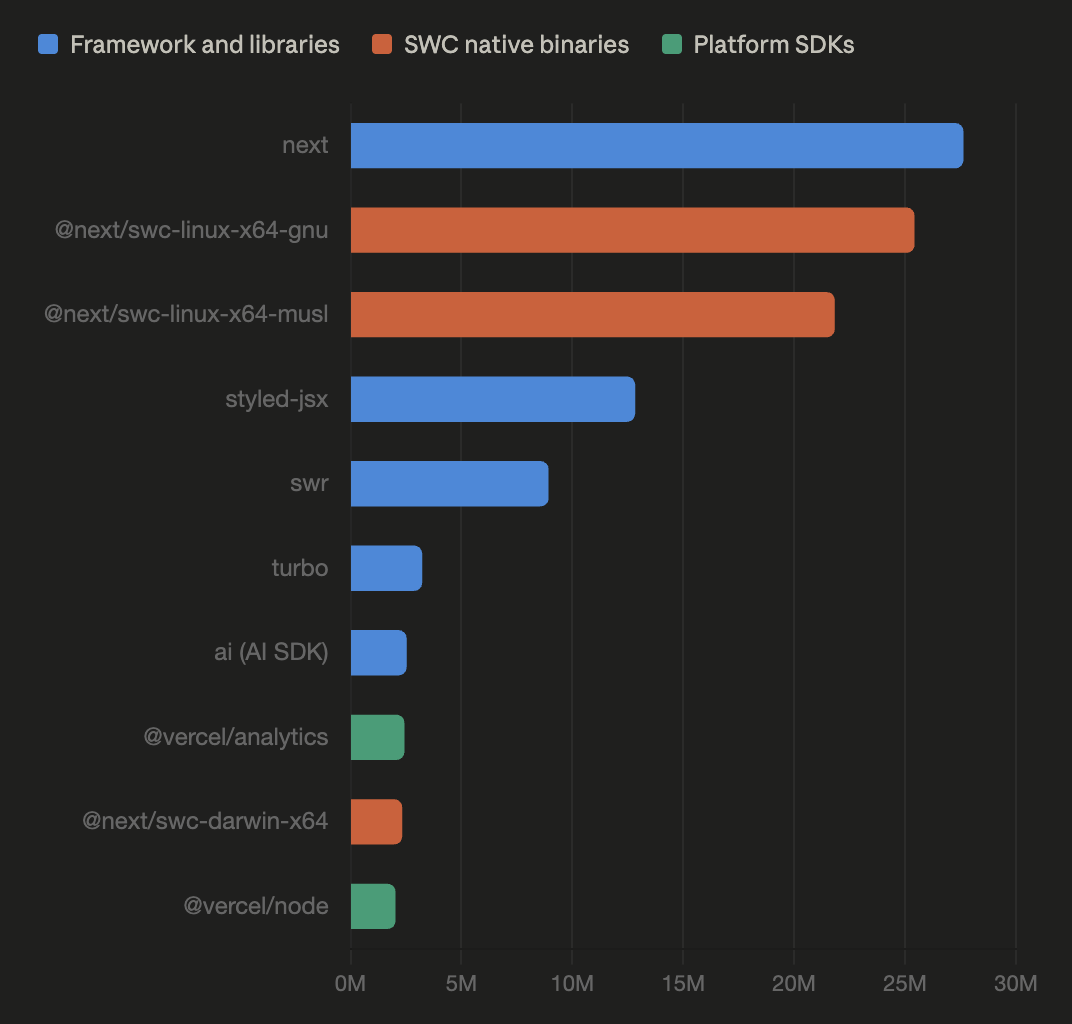
Vercel sits in the middle of a huge chunk of the JavaScript ecosystem. They maintain Next.js. Their customers include crypto frontends, Web3 wallet interfaces, SaaS dashboards, and marketing sites for companies you have heard of. A single compromised path inside Vercel can touch:
- Customer source code sitting in connected GitHub repos
- Environment variables (database URLs, third party API keys, auth secrets)
- Deployment pipelines that push production code
- NPM publishing credentials for packages Vercel maintains or participates in
- Internal tickets in Linear that describe ongoing security work, unpatched bugs, and architectural decisions
If even a fraction of the claimed token set is real and usable, the blast radius goes way past Vercel’s own perimeter. A valid GitHub token with write access to a popular package repo lets an attacker plant a malicious commit. A valid NPM token lets them publish a poisoned version of a dependency that thousands of downstream projects will pull on their next install. That is textbook supply chain compromise, and it is the nightmare scenario people are talking about when they say “massive ripple effects.”
To be clear, as of the afternoon of April 19, nobody has shown public evidence of a malicious package publish or a tampered release tied to this incident. The supply chain risk is probable rather than confirmed. But the confirmed part, the internal breach itself, is already enough to justify a pretty aggressive response from anyone with credentials connected to Vercel.
What the “sensitive env var” detail actually tells us
Vercel’s public recommendation to review environment variables and use the sensitive variable feature is doing a lot of work in a short paragraph.
The feature exists because regular env vars on Vercel live in a readable form for build and runtime processes, while sensitive ones are encrypted and access-gated. If the attackers got into systems where standard env vars were visible, any secret a team pasted into the dashboard without ticking the sensitive box is potentially exposed. API keys for Stripe, database passwords, private RPC endpoints, third party auth tokens, you name it.
That is the part that affects customers directly, regardless of what happens with the larger supply chain question. If you deploy on Vercel, you need to assume every non-sensitive env var you have set at any point could be in the wrong hands and act on that assumption now.
What to do right now if you deploy on Vercel
- Review the activity log on your Vercel account and environments for anything you do not recognize.
- Rotate every environment variable that was not marked sensitive. Do not wait for a notification email, do it now.
- Regenerate any GitHub, NPM, database, payment processor, or third party API credential that was ever pasted into a Vercel project.
- Turn on the sensitive env var feature for everything going forward that qualifies.
- Check your build logs for secrets that may have been echoed into output.
- If you publish NPM packages through a workflow that touches Vercel infrastructure, audit recent publishes and consider revoking and reissuing tokens.
- Look at your connected GitHub integration and check for any unusual commits, new deploy keys, or outbound webhooks you did not add.