Most engineering teams trust Axios without thinking twice.
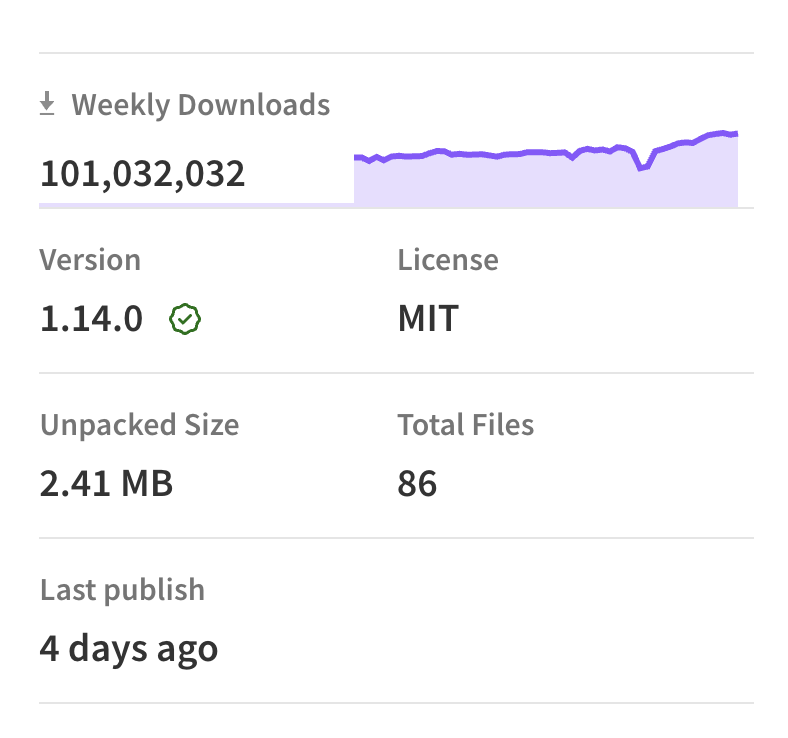
It is one of the most common packages in the JavaScript ecosystem. It shows up in frontend apps, backend services, CLIs, internal tools, and AI workflows.
That is what made the recent Axios incident so important.
What happens when a package that feels completely routine suddenly becomes the attack path?
That is the supply chain lesson here.
ELI5: what does Axios actually do?
Axios is a JavaScript library that helps apps talk to other apps over the internet.
In simple terms, if your frontend needs to fetch data from an API, or your backend needs to call another service, Axios is often the tool making that request.
It is commonly used for things like:
- loading user data in a web app
- sending form submissions
- calling internal APIs between services
- connecting apps to external platforms like Stripe, OpenAI, GitHub, or Slack
That is why it is everywhere. If a package like Axios gets compromised, it can land in a lot of places very quickly because so many teams install it as part of normal development.
What happened
On March 31, 2026, two malicious Axios versions were briefly published to npm:
axios@1.14.1axios@0.30.4
Public reporting indicates this happened after a maintainer account was compromised. The malicious releases added a dependency, plain-crypto-js@4.2.1, which was not part of normal Axios behavior and was identified as the delivery path for malware. Security researchers described the payload as a cross-platform remote access trojan affecting macOS, Linux, and Windows.
The bad releases were removed quickly, but any environment that pulled them during the live window should be treated as potentially compromised.
Community warnings spread fast because this kind of attack lands exactly where developers move quickly. One Reddit post aimed at Claude users put it simply: if you were "vibe coding" and ran fresh installs without checking, you should review your lockfiles immediately.
A package like Axios can reach:
- developer laptops
- CI runners
- production builds
- internal tools
- generated code from AI assistants
- container images built from fresh installs
That is what makes this kind of compromise dangerous. The issue is not only that a package was bad for a short period of time. It is that the package sits in places teams trust by default.
How the attack was constructed
This was not a typosquat or a rogue transitive dependency slipping into a build. The attacker had direct publishing access to the official Axios package on npm, likely through a compromised maintainer account. According to a collaborator in the official GitHub issue thread, the suspected compromised account belonged to a maintainer whose repository permissions were higher than those of other collaborators, which made rapid remediation harder.
No Axios source files were modified directly. Instead, the attacker added a pre-staged malicious dependency, plain-crypto-js@4.2.1, to the package.json of the new Axios releases. The plain-crypto-js package was purpose-built for this attack: a clean version (4.2.0) had been published 18 hours earlier, likely to give it a brief history on the registry and avoid suspicion. Version 4.2.1 contained the actual payload.
When a developer or CI system runs npm install axios@1.14.1, npm resolves the dependency tree, pulls plain-crypto-js@4.2.1, and automatically executes its postinstall hook: node setup.js. That single script execution is where the compromise begins.
The dropper: double-obfuscated and self-erasing
The setup.js postinstall dropper used two layers of obfuscation to avoid static analysis: reversed Base64 encoding with padding character substitution, and an XOR cipher with a hardcoded key and constant value. The goal was to make the payload invisible to automated scanners parsing for known malicious patterns.
Once deobfuscated, the script detects the host operating system and reaches out to a command-and-control server to download a second-stage payload appropriate for the platform. This is what security researchers identified as a cross-platform remote access trojan.
After execution, the malware cleans up after itself. It deletes setup.js, removes the package.json that contained the postinstall hook, and replaces it with a clean file that was pre-staged as package.md. If you inspected node_modules/plain-crypto-js after the fact, you would find no obvious sign that a postinstall script had ever been there. That is what makes this particular attack harder to catch through manual review alone.
What teams should do right now
If your team uses Axios, the safest move is to check immediately.
Start with the basics:
- Do not use
1.14.1or0.30.4 - Check lockfiles, build logs, and recent installs for those versions
- Look for
plain-crypto-js@4.2.1in dependency trees or build artifacts - Audit CI jobs, containers, and developer machines that may have pulled fresh installs during the affected window
- Rotate any secrets that may have been available in those environments
- Review unusual outbound network activity or suspicious processes after install
If those versions were installed in CI, on a developer laptop, or in a build container, it is safest to assume credentials in that environment may have been exposed until proven otherwise.
This incident is a reminder that highly trusted packages deserve the same level of attention as high-trust infrastructure.
A common HTTP client may look harmless because it is familiar. But when it sits across apps, services, and build pipelines, a compromise can spread quickly through normal engineering activity.
That is why teams should be stricter about:
- pinning and reviewing dependency updates before broad rollout
- using lockfiles consistently across local and CI environments
- watching for unexpected new transitive dependencies
- limiting secrets available during install and build steps
- treating fresh installs in CI as part of the attack surface
Add one simple defense today: delay brand-new package versions
This is one of the best practical tips from the Reddit threads today.
Set a minimum release age or cooldown before your builds accept freshly published packages. Example shared by developers:
npm config set min-release-age 3That means a package has to be at least a few days old before it gets pulled automatically. It will not stop everything, but it helps a lot against "compromised maintainer publishes malicious version for 2 hours" type attacks.
Takeaway
The Axios incident is a reminder that even the most familiar package can become a supply chain event very quickly.
When something like this happens, the first real question becomes: what is the blast radius?
Which repos pulled it? Which lockfiles captured it? Which containers baked it in? Which CI jobs installed it? Which developer machines ran it? Which secrets were present at the time?
That is where visibility matters. In Prismor, this is the kind of question teams should be able to answer quickly through the inventory view: where a package version exists, which repos and services depend on it, what environments it reached, and how far exposure can spread once trust breaks.